
I figured I'd wait until after my paternity leave was over before I started thinking seriously about words like "control" and "compliance," but I felt the need to say something after reading Bejtlich's post "Controls are Not the Solution to Our Problem."
He illustrates through citing an example of a control, and identifying ways that it fails to achieve total effectiveness. The control may not work and could be superfluous. His alternate approach is a system of assessments, tests and monitoring coupled with a rigorous set of metrics.
If someone describes an asset as "secure," "safe" or "reliable," my job as an auditor is to ask the question "How do you know?" The answer is a control. Bejtlich's "field-assessed" approach is another set of controls, mostly detective rather than preventative. What happens when his approach is codified into a government procedure or a vendor contract? A security practitioner with a preventative approach could grouse about how these pen tests and honeynets don't address the security needs in his shop (due to scale of operations or type and level of risk).
Tossing out controls is also just not an option. Effective or not, compliance keeps you out of jail. I don't always feel that on some roads a 55 mph limit is a necessary control to prevent accidents, but that will mean I am not breaking the law when I speed.
I'm not as big a proponent of metrics as a control solution, but I'll leave that to another post.
Tuesday, November 27, 2007
Confusion In My Eyes That Says It All
Posted by
Dutcher Stiles
at
1:56 PM
0
comments
![]()
Labels: compliance, controls, internal auditing, risk assessment, risk management
Tuesday, October 23, 2007
Tonight, We Dine in Utica!
So, despite a workload that would stun an ox, I still manage to read my Internet privacy stories. Like this one from Ars Technica about the University of Utica and their Secret Service data wrangling on identity theft.
I click over to the .edu to read what they had to say in the original text. But, curiously enough, they asked me for my contact information. Well, o.k. - but what is your privacy policy? I hit the link to their privacy policy. This is madness!.  No. This Is Utica!
No. This Is Utica!
Posted by
Dutcher Stiles
at
7:27 PM
0
comments
![]()
Labels: Everyday Privacy and Security, identity theft, privacy
Wednesday, October 3, 2007
Island of Lost Laptops

Why are people still all wound up about losing laptops? For crying out loud, there's a reason why the press doesn't report about it anymore. Because it is Bo-Ring. I mean, I'm putting myself to sleep just typing this.
What I want, nay, what I demand is in-depth reporting on what happens to the laptops after they are lost. Gimme some intrigue, some action, and a taste of science gone horribly wrong. I'm guessing there's some island somewhere, a man with a whip and a SOX auditor's idea of discipline, and a crew of sad... well they're not Dells and they're not Compaqs, they're things. Toss in the seductive animal lure of the Apple OSX 10.3-woman, maybe a house of pain or two. Now we're talking.
Auditor: What is the law?
Regulator: Not to spill data. That is the law. Are we not men?
But, as you can see below, strict compliance to standards does not alway result in a social benefit.
Posted by
Dutcher Stiles
at
3:53 PM
0
comments
![]()
Friday, September 7, 2007
Howls of Derisive Laughter, Bruce!

By now, we all know that the concentric perimeter devised by the kangaroo jockeys assigned to protect the best and brightest of Asia and the Pacific were ineffective against comedian pranksters. (Perilocity has the lowdown.)
But what if they had been REAL pranksters? The NYC could teach those koala huggers a lesson in deterring those cats. They successfully defended the Republican National Convention against a variety of threats ranging from partial nudity, Johnny Cash impersonators, poetry, wet T-shirts and rock 'n roll. I'm confident that a couple of pranksters with a Canadian flag and a limo would not have escaped the attention of The Finest, and would have at least one entry in a database. And, oh, yes, their data would be aggregated, sooner or later. Yes.
I guess my point is two-folded:
1. A system meant to trap terrorists may not trap your prototypical Prankster 2.0, just as a system designed to trap thieves may not trap auditors. (I believe I have railed on this before.)
2. A system meant to trap terrorists may also trap Johnny Cash impersonators.
Posted by
Dutcher Stiles
at
4:16 PM
1 comments
![]()
Labels: physical security, privacy, threat, wattle
Wednesday, August 29, 2007
Compliance for Road and Track
 My Alfa, a 72 GTV coupe, like all GTVs of its approximate vintage, has a recessed panel in the headliner over the back seats. It has proven to be a mystery to passengers in the car, looking like the cruelest joke of a sun roof for the rear passengers who are otherwise treated poorly by the car's design. So cruel, in fact, that a sticker was placed on the rear windows by Alfa. When viewed from the outside, it read:
My Alfa, a 72 GTV coupe, like all GTVs of its approximate vintage, has a recessed panel in the headliner over the back seats. It has proven to be a mystery to passengers in the car, looking like the cruelest joke of a sun roof for the rear passengers who are otherwise treated poorly by the car's design. So cruel, in fact, that a sticker was placed on the rear windows by Alfa. When viewed from the outside, it read:
GROUP 2 TOURING CHAMPION 1971
EUROPEAN MANUFACTURES SERIES
This side of the sticker explains in part the pseudo-sun roof. The GTV raced in the sedan class. To comply with sedan class regulation, there had to be a specific number of inches of headroom for the two passengers in the back seat. Hence the "cheat" of recessing a spot in the headliner, because the seats were as low as they could go. So you can race, and sometimes beat, Minis, BMW 2002s and Datsun 510s.
From the inside, the other story of compliance was visible. From a knees-to-chin head-ducked position, the contorted rear seat passenger could read the obverse:
TO BE OCCUPIED BY PASSENGERS
WHILE VEHICLE IS IN MOTION
The other set of regulations the GTV had to comply with were written by the US Department of Transportation, that defined of sports cars and sedans. Being classified by the DOT as a two-seater would require less modification of Alfa's aging (yet still stylish) design - less in the way of bumper protection for the would be passengers. Actually taking the seats out and putting in a package shelf (a la 911) would make it race in an uncompetitive class. Hence the sticker forbidding rear seat passenger, which attempts to serve both masters. (I'm guessing the seat belts back there are for securing cases of Chianti and bundles of pastrami.)

The different approaches in compliance reflect the different levels of enforcement. Perhaps Alfa felt it could convince the DOT that, really, who would ever be so silly as to sit back there? This is a sporting coupe, not a sedan. However, Alfa knew that the sanctioning bodies for the racing series they participated in would be out there with tape measures and calipers before every single race for tech inspection. Alfa's compliance would be challenged by every other team on the track.
I don't believe it would be too far off the mark to say that an implementation of a control, especially a compliance control that may not have a palpable financial return, will be as effective as the perceived enforcement.
(Read the story of the 2.5 liter Trans-Am at 1971 Laguna Seca for more sad stories of compliance. The Datsun version, the Alfa version. "Oversize fuel lines" vs "expanding gas tanks." )
(sticker image courtesy Papajam at the AlfaBB)
Posted by
Dutcher Stiles
at
4:38 PM
2
comments
![]()
Labels: alfa, compliance, internal auditing, motorisk, risk assessment
Tuesday, August 21, 2007
Market Fresh

A curious discussion of terror risk, and a terror prediction futures market by some GMU economist types and at the Chronicle's Footnoted blog.
I don't know enough to about econ to assess the value of such a market, but I do wish that some one would set up a Privacy Breach Futures Market so we could make the security analystas put their magic quadrants where their mouths are. (Or vice versa: whichever would be more unpleasant.) Viz, the TJX OMG!!1! MILLIONS IN PWNAGE!! NO!!BILLIONS! analysis found on Computerworld. Maybe something more along the lines of buying squares in a football pool would offer as much predictive value as the collective voices of these cats.
Photo courtesy The Prodigal Son.
And yes, this is the second consecutive post with a Broken Social Scene related title. Because Broken Social Scene are one of my top five most favorite things that are Canadian.
Posted by
Dutcher Stiles
at
5:17 PM
0
comments
![]()
Labels: breach notification, disclosure laws, risk assessment, risk management, threat, vulnerability
Monday, August 20, 2007
I Feel That It's Almost Crime

Imagine Monster put a click-through license on the malware, adjusted the privacy policy a tad (include an opt-out for additional "services"), and voila! It's not a privacy breach, it's an additional revenue stream! The 1.6M bits of Monster job hunter data is at least as hot as the Glengarry leads.
Imagine that Certegy/Fidelity records were not sent in wild cascading romp through the land of data brokery by the actions of a rogue database administrator, but through a perfectly legal contract. (As Mr. Certegy assures us, the data was sold to legitimate data brokers.) So the whole thing is a just a crossed "T" or dotted "I" away from being 110% on the up and up. Instead of class action, we'd be talking steak knives and Eldorados!
It's just semantics. "Data broker" = "Identity Thief." "Lead Generation" with "Privacy Breach."
It's all the same. But the Yukon keeps me up all night, and it feels like it's almost crime.
Posted by
Dutcher Stiles
at
4:14 PM
0
comments
![]()
Labels: breach notification, consumer, disclosure laws, identity theft, privacy, singalong
Wednesday, August 15, 2007
Everyday Privacy and Security: Buying Age Restricted Products

So, I go into an Exxon, looking to buy a pack of butts. (An evil, nasty habit I am trying to quit, but the demon weed still has its claws in me.) I ask for a pack of what they had that was closest to my brand, and it was slapped on the counter. Then the clerk asked for my ID.
O.k. Tobacco, along with pornography, beer, and sometimes phen-phen, is an age restricted product available at some convenience stores/gas stations. Despite my advanced grizzledness and paunchitude, and my sincere doubt that the woman behind the counter was trying to flatter me by insinuating I could be mistaken for a teenager, I complied.
And I was ready. I had recently traveled by air to San Francisco, renewed my license, but still had the printed paper companion from the DPS to accompany my laminated driver's license with an older, but still somewhat grizzled image of my mug on it.
No dice. My license was expired, therefore I was probably under 18. The fact I had renewed my license was no good. "Policy," the woman said. "But....But..." I objected. "Policy."
In my nicotine deprived state, muttered my way back to my car, curses ranging from Kip Hawley to Captain Hazelwood. And of course, the X-Ray Spex wormed into my brain:
IDENTITY IDENTITY IDENTITY
Posted by
Dutcher Stiles
at
4:03 PM
0
comments
![]()
Thursday, August 2, 2007
Impacted Molars: Pay Hell Gettin' It Done Edition

Random Eye-tooth:
I've been reading the Counterinsurgency Manual, and I'm figuring there is some analogue to a corporate approach to minimize the "insider threat."
Extraction:
Mr. Loblaw describes a grisly example of privacy abuse in a recent decision du jour, selecting the choicest text of a 6th Circuit decision so I don't have to. But I will.
As the plaintiffs’ complaint explains, prisoners have threatened and taunted the officers, often incorporating the plaintiffs’ social security numbers (which they have committed to memory) into the taunts. Some prisoners wrote the social security numbers of some of the plaintiffs on slips of paper that they threw out of their cells.Now that's what I call abuse of NPI, a sort of SSN gassing. But do the plaintiffs get relief? No.
[T]he guards’ social securities numbers are not sensitive enough and the threat of retaliation from prisoners was not substantial enough to warrant constitutional protection.Ride the NPI Country:
Courtesy the continual compendium of outrages privacy related, i.e, Pogo, come this story hashes ID crime stats. The conclusion it appears to draw is that Big Sky Country is a den of ID thieves. All the big increases in identity crime occur in North Dakota and Montana, with the notable exception of Springfield, IL, which can be attributed to Groundskeeper Willie and Apu. Considering that there are more people in my MSA than all of Montana or North Dakota, I wish I could get a thorough look at the stats. Not so bad that I'm going to request data from a "marketing@" e-mail address, which ID Analytics requires.
Computer Security for Trainables:
From the Chronicle tech blog, the winners of Educause's security awareness video contest. I dunno. These videos will not be a part of my infosec counterinsurgency program. No beat, can't dance to 'em.
Bonus:
"Sweet fancy moses": the whole shocking story. Discuss.
Posted by
Dutcher Stiles
at
5:05 PM
0
comments
![]()
Labels: best practices, crime, fraud, identity theft, insider threat, privacy, ssns, teeth, war
Wednesday, August 1, 2007
Describing Difficult Procedures

Lately, I've been working on my 1972 Alfa Romeo GTV. What I've learned about project management seems to evaporate into red mist in my garage. Currently, as part of changing my fuel system from the wonderful yet arcane SPICA mechanical fuel injection to the elegant and infinitely adjustable Weber carburetor, I am pulling the head off the twin overhead cam beast.
The head pulling process is described in the Alfa Romeo Giulia Owners Workshop Manual thusly:
"Remove the head nuts and the two screws fixing the front cover to the head, then lift off the head."
As it represents the official, legally vetted process described by the vendor, the above advice can be called "the standard."
Pat Braden's definitive "Alfa Romeo's Owner's Bible" describes the procedure thusly:
"The head bolts should be loosened incrementally following a spiral from the center out. Work slowly around the engine double-checking that everything is removed before trying to lift the head free. Typically, the head won't come free."
This passage is followed by several paragraphs of recommended procedures for freeing the stuck head, including "factory tool" and "rope trick." Having been codified in book, written by an expert, these are clearly "best practices."
On the Alfa Bulletin Board, a search on "head removal" will generate a multiple page jeremiad of head pulling frustration and anxiety. Tools as diverse as crow bars, bottle jacks, concrete rust remover and improvised pullers are deployed to extract head from block. Results vary. I'll call this "how things happen in real life."
Posted by
Dutcher Stiles
at
9:53 AM
0
comments
![]()
Labels: alfa, best practices, standards
Wednesday, July 18, 2007
Half Baked

What follows are annoying thoughts that have been ground to meaningless gravel in my head for the past month or so. As soon as I think them through, and dismiss them, my brain belches them back up. Committing them to the ether seems the only way to purge them, but I've been wrong before:
Proximity and Privacy: Privacy breaches due to negligence occur when there is a distant relationship between the identity custodian and the individual. Malicious breaches occur when there is a close relationship between the two. (Half baked corollary: Web applications proxy a close relationship with distant actors.)
Metrics Will Be Juked: The compiling of stats is the prelude to the inevitable juking of stats. Observing, recording and reporting the data underlying a performance metric corrodes its value. The reason data that is difficult to access and compile is compelling is because it is difficult to access and compile. Once people realize that their behavior, or the results of their behavior are being observed and measured, their behavior will change, not necessarily to impact the desired results, but to change the metric. This change will be multiplied if the measure is tied to compensation or perceived to be tied to compensation.
Lone Gunmen Theory of Privacy Risk: Measuring a corporation's loss due of breach of privacy is futile and meaningless. This loss is not related to the harm to individuals whose privacy was violated. It makes no difference if the data is lost, stolen, or sold, or if it occurred within or without the bounds of the law. I don't see any equation that will match corporate postage, legal fees, data broker accounts receivables, or public relations consulting with personal financial trials, embarrassment, loss of employment, prohibition of travel, or physical detention. Privacy risk is borne by individuals, not corporations. Which is why I was a bit distressed when I read this:
If you are not suffering any damage due to these breaches, then why are you even trying to deter, detect, and respond to them in the first place?In privacy, it's always the other guy that suffers the real damage.
Now I can concentrate on the important things: sorting out my emotions regarding the preemption of TV coverage of the German GP by live broadcast of Lady Bird's burial and Laguna Seca.
Posted by
Dutcher Stiles
at
6:36 PM
0
comments
![]()
Labels: breach notification, compliance, internal auditing, risk management
Monday, July 16, 2007
Privacy is a Technological Imperative

My seasonal July funk has been working on me and my attitude, but not so much that I can't find some perverse humor in the slashdot discussion on privacy as a biological imperative.
Ms. Sweeney's correlation of privacy to the stealth required by the predator stalk and consume prey was latched on to by the /.ers like an antelope at a watering hole. I don't see it myself. There is a fundamental difference between the biological need to eat and personal need for privacy. The development of information technologies creates the need for personal identity, and creates the tools to destroy it. Examples include the portable camera (which drove Warren & Brandeis to define the right to privacy in the context of the US Constitution), the telephone, punch-cards and TCP/IP.
These aren't new or original thoughts, but just how I see it.
Lion enjoying a private moment courtesy hannes.steyn.
Posted by
Dutcher Stiles
at
2:58 PM
0
comments
![]()
Labels: privacy
Wednesday, July 4, 2007
The Easy No

From Concurring Opinions, this commentary on a recent New York Times article on Hypercompliance on the HIPAA front. Health care folks have been intimidated into denying access to PHI to people who have legitimate inquiries and a legal right to it.
This type of behavior is born out of fear and poor understanding of rules filtered through complicated reports written by obfuscating contractors. It seems reactionary, and unreasonable, but a means to the safety only an ass well-covered provides. As Mr. McGeveran points out, "it is always easier to say 'no' than to figure out how to say 'yes.'" I believe mistaken "safe" attitudes like this is often how security policies end up being implemented, and are difficult to purge once they become corporate folklore.
The "easy no" is not uncommon in security management, and enables ten thousand wannabe Kip Hawleys to exercise passive aggressive nonsense in its name.
Beats thinking.
Posted by
Dutcher Stiles
at
10:09 AM
0
comments
![]()
Labels: compliance, regulations, security
Wednesday, June 27, 2007
Dog of War or McGriff the Crime Dog?

So, solider or cop? War or Crime? Or both?
I ask this question of my own self after reading (and enjoying) Michael C. W. Research's recent posts on security framed in the context of Clauswitz. Thinking it through, though, I began to wonder if war is the context information security should frame itself. After all, as an info security practitioner, you are denied both first strike and retaliation with like force. Hampered by a bureaucracy, limited by budget and laden with metrics of questionable value, you perform awareness and outreach to a resistant, often resentful community that harbors potential adversaries. When the adversary attacks, your response is defensive, forensic, and heavily regulated. In the initial analysis, it sounds more like a cop than a soldier.
Like Mr. Peterson, I recently finished reading Robb's Brave New War. Robb describes the decline of wars between states or their proxies and the rise of the global guerrilla. The global guerrilla uses system disruption and open source warfare to break down the brittle security systems of organized and highly interdependent states. Mobile and rapidly adapting to changing tactics, this adversary is usually hidden in the state it is trying to hollow it out, cooperating with or participating in transnational organized crime. Now that threat sounds more familiar; Robb describes the phishing marketplace as a example of open source warfare.
Is War now Crime? Is the infosec defense model Clear Hold Build or Broken Windows?
Posted by
Dutcher Stiles
at
3:49 PM
0
comments
![]()
Labels: crime, global guerrillas, security, threat, war
Tuesday, June 19, 2007
New Concepts in Data, Compliance and Marketing or The Overly Dramatic Truth

Like the rest of the world, I read J. Cline's article on the upcoming data eclipse while listening to El P's I'll Sleep When You're Dead, which is the best way to read it.
J. Cline is prophesyin' the impending darkness where all corporations will crumble 'neath the cleated boot of data governance.
Mr. Cline identifies the signs of the data eclipse endtimes: Ford has abandoned autos to focus on quality improvement. Wal Mart has unburdened themselves of the lucrative Chinese tube sock trade for supply chain management. In the post-eclipse world, we must surrender control of our enterprises to the wanton desires of regulators, lawyers and audit chimps such as myself. We no longer make the decisions, but wait for them to be passed down from these distant parties who ponder our fate far from the red meat and hot breath of corporate operations. It's not the moon, after all, but the pointing finger of compliance and legality we should focus on.
I may have been born yesterday, sir, but I've been up all night. Like a diamond bullet between the eyes, I was struck with an aces-on Notion (with a little backing I think I could turn it into an Idea) which will make me the fortune I frankly deserve. A methodology that will empower the document generating wherewithal of ten thousand legions of certified information control professionals.
I will call it the Compliance Legal Object Audit Client Architecture: CLOACA. Look for my booth at a tradeshow near you.
CLOACA: You'll Be Surprised What Can Come Out Of It!
Posted by
Dutcher Stiles
at
4:22 PM
1 comments
![]()
Labels: compliance, El P, internal auditing, logic, regulations
Tuesday, June 12, 2007
Vulnerabilty v. Threat
Jeremiah Grossman's analysis of the MSNBC stock contest cheat.
It seems to me that this sort of flaw would rise to the surface quickly from a threat perspective, but slower from a vulnerability perspective. I'm not sure why though.
Posted by
Dutcher Stiles
at
5:09 AM
2
comments
![]()
Labels: compliance, security, threat, vulnerability
Monday, June 11, 2007
The Italian Job

Odd ball kidnapping heist documented at MCN and Roadracing World illustrates the danger of the insider beyond the pilfered laptop or unexpired system credentials.
Apparently the Alto Evolution World Superbike team "reduced the responsibilities" of Sergio Bertocchi, their erstwhile manager, after the race at Monza a while back.
On the way back to Italy from the most recent race at Silverstone, UK, the Alto truck gets hijacked at a border crossing. According to the Alto Evolution press release:
The driver was kidnapped for more than six hours and the truck diverted. The driver was able to escape in Bruxelles - Belgium, where he alerted the police and confirmed the names of the people of the gang which had kidnapped him and stolen the truck. Amongst the members of the gang have been recognised four people: one of them was Mr. Sergio Bertocchi.
Policemen from Belgium have immediately started investigations and, at the same time, Carabinieri in Italy have been alerted. Investigations have gone on strenuously and with outmost secrecy. On the 6th a van of ours was sent to Trieste to recover other spare parts and accessories still in Trieste's warehouse. On the way back, in the first rest/service area out of Trieste, the same criminals have stolen the van and its content. Unluckily for them, following a great effort of electronic interception and lots of their's tailing, law-enforcement personnel has had the opportunity to see the criminals in action in first person. Carabinieri have been on the van's tail for a couple of hours and at last they have recovered the vehicle and its content and put them under sequestration.Although it reads as if they got Alto's rider Muggas to do the translating directly from Italian to Tweed Headsian blindfolded, at first blush appears to be a story of justice served. The former manager plays the archetypical role of the disgruntled employee who turns against his employer by hacking, vandalizing, stealing office supplies, truck hijacking and/or kidnapping. His fiendish plot is foiled due to surveillance and electronic tracking. Chalk one up to the gallant carabinieri and their high tech tracking equipment!
Meanwhile the subject liable for theft have been blocked. On Friday the 8th Carabinieri have given us communication that the truck has been found and is now in a safe place in Trieste, again judges have disposed sequestration of the goods.
And interesting question regarding identity, though. Did former manager Sergio use his identity to gain confidence and access to the truck? Seems that would be an enormously boneheaded maneuver for a hijacker. I've got issues trying to correlate the motivation of the attacker with his techniques.
Maybe it was just a denial of service attack. Check that word "sequestration" in the above quote, on which the Alto Evolution team elaborates:
This, and only this, is the reason for which we will not be able to partecipate to the race in Misano on the 17th of June.Not too difficult to imagine Sergio in his Italian jail cell rubbing his hands together, mumbling about how they'll never race in Misano...never in Misano..
Posted by
Dutcher Stiles
at
6:16 PM
0
comments
![]()
Labels: insider threat, motorisk, security, wsbk
Thursday, June 7, 2007
Sufficiency, Competence, Relevance

I returned to work after a refreshing and invigorating vacation in Wisconsin and greater Chicagoland. After marking random e-mails as "Read," I look over some notes I took in a prefreshed state, most particularly this line:
"Reality vs. ????"
I figure I was on track to bust my epistemological crisis wide open, and instead I caved into some ontological audit chasm. Not quite a zombie, but brains are starting to smell real good.
"Reality vs. ????" I think I was getting into a Rashomon fugue state, with folks skating around conflicting stories, but nodding in agreement. I wanted to know: When evaluating perception, what evidence is more reliable than testimonial evidence? Is the written as as important as the thought which drives the action? Can or should the common testimony of a dozen individuals be sufficient to assert a common perception, and be used to predict a likely action?
I searched the Red Book and Yellow Book for the answer. To make sure I didn't miss anything, I checked the Blue Book, too. (Man, that Mazdaspeed3 looks SWEET!) Their answers rang as hollow as a Sturtevant kringle, just not as tasty. "Sufficient and appropriate," "competent and relevant," "better if supported by documentary evidence," "yada yada yada." Not helping me out.
I was looking in the wrong places, of course. In my backpack was the unfinished beach reading: King of the Jews by Nick Tosches. I dig Tosches in a serious way; he is a relentless researcher with a full appreciation of the negative case. From the Book of Esther to Abe Lincoln to Mayor Bloomberg, Tosches makes clear that evidence - competent, appropriate, sufficient or otherwise - winds up as whatever is said most often, and what is said most often is often enough wrong. Still not much of an answer. Really sort of grim.
Nonetheless, with that cryptic fugue out of my system, I'll go back to work. Less episteme, more hax0rme.
Posted by
Dutcher Stiles
at
7:55 PM
0
comments
![]()
Labels: arnold rothstein, internal auditing
Tuesday, May 29, 2007
The Red Duck

Yesterday was a tough one at work, made especially tougher by the fact that the House of Tooth is flying out on vacation tomorrow, earlier than I feel comfortable contemplating.
But if Mr. Howell is going to write about motor vehicular risk, so will I.
When I got home last night, I watched Race 1 of the WSBK at Silverstone. Nasty conditions: standing water on the track, filthy visor-coating mist flung up from rear tires, cold rain, poor visibility, and very heavy very aggressive traffic. So nasty that the second race was red flagged. Sounds like Chandler's Chicago commute, with the following exceptions:
- Everyone is on two wheels (except for the Alfa 159, which follows only on the warm up lap, and at a discrete distance).
- The cycles have been freshly massaged by well paid mechanics, sparing no expense in picking the fly poop from the pepper in handling, power delivery and suspension according to the desires of the rider. When the track is hot, statuesque women in high heels hold umbrellas over the motorcycles to keep them cool.
- Everyone on the track is wearing leathers, gloves, boots, back protector and a full-face helmet.
- No one is chatting on a cell phone or drinking coffee whilst riding round the track. The only communication is through flags waved by officials and corner workers, and the pit board with a couple of numbers hung out for the rider to read as he speeds past. None of this NASCAR-style chit chat and sippy cups.
Are strictly enforced regulations and technical innovation what makes for great racing? Is it all physics, themodynamics, fluid mechanics, geometry and friction?
No. What makes for great racing is the fact that these machines are piloted by the world's finest chaos generating engines, i.e., motorcycle road racers. Otherwise, why does nutso "Nori" get wear a rainbow wig on the podium, while his stoic Wollongongian team mate does not? What is to prevent a twitchy Frenchman on an equally twitchy Kawasaki from having a fleeting existential moment, resulting in a high velocity green missile smashing into a focused Texan's perfect line round Ascari? Nothing. The black swan rides the track along with the red Ducks.
Like any enterprise, you can comply with the regulations. You can follow the rules. You can become technically innovative. But the enterprise is run by chaos driven humans. All you can do is strap them in leathers and hope they don't lose any more fingers than is absolutely necessary.
Posted by
Dutcher Stiles
at
4:58 PM
0
comments
![]()
Labels: bayliss, ducati, motorisk, risk management, wsbk
Tuesday, May 22, 2007
Signals, Calls and Marches

Two stories stuck in my craw this past week. Now, I'm spitting them out, for your pre-masticated pleasure.
Firstly:
Tim Wilson's post at Dark Reading figures we shouldn't buy IBM security services because one of their contractors lost a storage tape with NPI on it. And that a public wireless company should not be patronized because they had a crooked options administrator. The TSA loses some employee data, so what..? We find some off-brand liquid & gel manhandler? The causality between the security products and services offered and the lapses in security and anti-fraud controls seems spurious. Does TJ Maxx not still shop continuously so I can find fabulous fashion bargains? That I'll pay cash for?
Segundo:
I can't believe the guy playing Punk'd with Google AdWords got so much press. The SANS dudes creamed themselves into a fit self-righeous suspender-snapping ecstacy in their newsletter over this DARING SOCIAL EXPERIMENT! The story was lame, proved nothing, but did allow the SANSabelters a chance to feel so superior to the l00zerz that would click on a link that says "Infect your computer." All that energy parsing stats THAT MEANT NOTHING! Dismissing your customers as ignoramuses, and pointing to practical jokes as proof is no way to run a "profession." If you must, at least do it behind closed doors.
Cause in the words of Mission of Burma:
So make sure that you are sure of everything I do
'Cause I'm not, not, not, not, not, not, not, not your academy.
Posted by
Dutcher Stiles
at
5:38 PM
0
comments
![]()
Thursday, May 17, 2007
Motoprox

Yesterday I was barreling down the concrete slab choked with tractor-trailers and nitro-burnining funny trucks laden with oily 2x4s and spent joint compound jugs, I was engaging my left brain in random problem solving ("Resolved: The world is as random as it is not.") and engaging my right wrist in focussed throttle control on my Triumph Bonneville. I hate the road - a stretch of oversubscribed interstate that at an unfamiliar time (around 3:00 pm) and was unfamiliar with how the traffic would be flowing. The part of the brain that controls motorcycle function became increasingly engaged.
Fortunately, it didn't come out of nowhere: some set of clues were processed so I was pretty sure the black sedan was going to dart into the part of highway I was occupying. I braked as much as I could, as the pickup behind was riding my exhaust, and I moved as far to the left of the lane as I could. Just as his door was nearing my knee, the driver of the sedan spotted me, and made a panic swerve back to his lane. No harm, no foul, just a cortex soaked in adrenaline. People pay good money for that.
Which led me to my thought. Do near misses count?
UK Civilian Aviation Authority Airprox Board thinks so. They are dealing with potential accidents, however, with an not unreasonable assumption that neither party wishes a collision. There is no attacker, so it is easier to get both sides of the story, and a clearer, truer account of the incident, and quality information to improve the process. In a security incident, you will rarely get the other side of the story, so the account is skewed to what the defender has observed, and the attacker has failed to hide.
The Risk Management and Decision Process Center at the Wharton School has this brief description of its Near Miss Management study.
It may be nothing useful, but I'm wondering how "near miss" security incidents are handled. How are the elements of "luck" and "skill" (i.e, controls, response,etc.) allocated? Since the bullet was dodged, is there a increase in comfort in the level of security, even though it may have just been luck, or the actions of the attacker, that made it a "miss"?
I don't know, but I've been hyperaware of traffic lately, and my head is encased in Shoei and my body in Tourmaster. (And for more on motorisks, see Chandler's post from last September.)
Hot Honda on Duck action courtesy PhillC.
Posted by
Dutcher Stiles
at
4:54 PM
2
comments
![]()
Labels: motorisk, near miss, risk assessment, security
Monday, May 14, 2007
Everyday Privacy & Security Part 2: Fear Factor Authentication, or I Won't Forget You Baby, Even Though I Should
If you are like me, or, if in fact, you are me, your online financial transacting experience has gone all Security 2.0 by the factor of WOW!
Over the weekend, I had an unpleasant experience. The clerk at our local What-Nots 'N Such franchise denied me use of my cash card. I figured my financial institution was trying to protect me whilst humiliating me, so I scurried home and logged into my financial institution's websperience.
But! Wait! My financial institution has gone all Fort Knoxy on my ass since the last time I websperienced them. They want to really get to know me before I can check out my balance. It went like this:
Dude! We're all secure and stuff now. It may be a pain in the back-end, but you will thank us because we will know you better. It's all legal. As a matter of fact, we wouldn't even be doing this unless we had to, but banking is mostly about money, and partly about pretending. So let's pretend.
Please enter your account number.
O.k.. But, no, that was your SSN.
Wait. Ooops. O.k. Let's call it an account number for now and move on.
Here are some fun disclosures for you to read. I'll wait here whilst you peruse them. Our attorneys wrote them to be concise but with a hint of whimsy, sort of P.G. Wodehouse meets Sartre.
Done already? Man, took our lawyers a bit longer, but whatever. Let us begin.
Type in some random characters.
More... More.... TOO MANY.
Did you include some numbers? Try that.
And some non-alphanumerics.
O.k. Hope you remembered that. It could be your new password, or your new account number or what the tellers will whisper under their breaths when you come in to get a loan.
Now comes the fun part. To your right you will see pictures of six different semi tractor trailers. We're going to use these pictures to identify you in the future.
Please pick the truck that most resembles your maternal grandmother.
Interesting choice.
Now some questions. Answer using your gut, and pretend that this is just between you and us. We'll use these questions for something in the future, probably resetting your password when you realize that your keyboard doesn't have a cent symbol on it. But pretend it's a legit reason.
Answer the following to the best of your knowledge:
Your favorite color.
The brand undergarment you are wearing right now.
Your favorite place for making whoopee (City and State only, please!)
Your favorite Poison lyric.
Interesting. You know you just qualified for a boat loan the way you answered that last one.
Now just press enter. (I hope you have Javascript, ActiveX and are typing this from a Internet Explorer 6 on Windows XP cause else I don't know what's going to happen.)
Sorry! You chose the wrong truck. Let's start again. Hit the back button. NO, NOT THAT BACK BUTTON!
Microsoft OLE DB Provider for ODBC Drivers error '80040e07'
[Microsoft][ODBC SQL Server Driver][SQL Server]Syntax error converting the nvarchar value 'login_id' to a column of data type int.
/index.asp, line 5
Posted by
Dutcher Stiles
at
3:48 PM
2
comments
![]()
Labels: compliance, Everyday Privacy and Security, FFIEC
Tuesday, May 8, 2007
SSNS ON THE LOOSE! (Legacy Edition)
I'm trying to understand the newsworthiness of the latest episode of "SSNS On The L0OzE. OMG!!1!!"
Some dude in the mail room puts a bunch of computer tapes in the wrong slot, according to the AP report in the Houston Chronicle. State agency looks for 'em. Contractor looks for 'em. Then they find 'em, in the wrong slot. A problem as old as the mainframe.
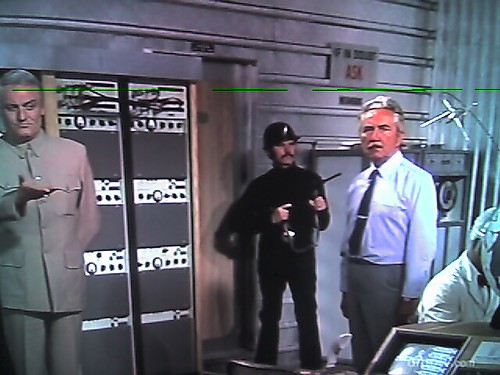
My guess: the missing tape was a quarterly report (WITH SSNS!!), there was some turnover in the computer room, and the folkloric control vanished with the last operator who performed it. The article doesn't state the format of the tapes, but I'm guessing it's EBCDIC flavored, with a chewy center of either DB2, Adabas or Model204. (The New Russian mob has standardized on Unicode, leaving behind Blofeld and his "legacy" villainy.)
Solution? Document the process, develop a tracking spreadsheet. People have been exchanging tapes for decades, and there are simple ways to track it. You could even buy some bar code software, or something. (As it says on the wall in the illustration: If In Doubt ASK".)
What is the solution proposed by the contractor?
The company is now exploring transferring the data electronically to improve security, [contractor spokesman] Lightfoot said.I think my way is cheaper. And safer. And easier to track. I only know what I read in the papers, though.
Diamonds Are Forever image courtesy Xeni.
Posted by
Dutcher Stiles
at
4:04 PM
0
comments
![]()
Labels: breach notification, disclosure laws, internal auditing, physical security, sb1386, security
Monday, May 7, 2007
Throwing Scorpion Out With the Frog Water

Declan McCullagh says that the federal government is unlikely to implement the National Research Council's privacy recommendations, in particular, a privacy commissioner, because it isn't in the federal government's scorpion-like nature. Ars Technica also has coverage. (And why must it always be a czar?)
The US is having the same issue with privacy legislation that it had with television resolution. We adopted early, because we needed to see our Felix the Cat on the airwaves, and 441 lines of resolution are all that NBC in 1941 could muster. Likewise, the privacy principles developed by the US government in the 1970s were developed too soon, when databases were just creeping out of the punch card era. US privacy law ends up like broadcast TV sets - an archaic lo-res standard, while other parts of the world lagged behind, but adapted a more advanced standard. Think of Europe's Privacy Directive as PAL.
From what I've read of the NRC's paper (the Executive Summary), it seems they are going for a full blown HiDef 1080p Dolby Surround sort of privacy regime. Just as the networks dragged their feet on the 441 lines of resolution until they were forced to move ahead with HD by the FCC, so will industry drag their feet on privacy until a privacy czar, prince or archbishop cajoles them into the 21st century. I'm being optimistic, but at least the frog was committed.
Lo-Res Felix from FelixtheCat.com
Posted by
Dutcher Stiles
at
3:49 PM
0
comments
![]()
Labels: privacy, regulations
Friday, May 4, 2007
Waffle are Just Pancakes with Little Squares On 'Em
I've been working on something, but I don't know if it will make by race time in Shanghai.
In the meantime, the most important part of internal auditing is "production value." And we know what that means.
Posted by
Dutcher Stiles
at
10:52 PM
0
comments
![]()
Labels: internal auditing, risk assessment, tapeheads, waffles
Tuesday, May 1, 2007
Impacted Molars
 Brighter Teeth
Brighter Teeth
From Educational Security Incidents via Pogo comes this terrifying story of privacy laden scratch paper from the land of the gigantic stone Texan. Apparently Sam Houston State U. uses a student ID number that is not their SSN. Hooray! But they do sometimes print out sheets that correlate the student ID with the SSN for the math lab to use as scratch paper. Boo! But this was strictly against policy, and was surely attributable to the Soviets since:
"After a security briefing last summer, we no longer use SSN's, we only use Sam ID numbers to keep Identity Fraud down," Harris said. "It is against the University's procedures to use SSN, so if it prints off, we automatically white the information out." [emphasis all mine]Teacher's high indeed!
Fresher Breath
From Dark Reading, a grim story of my home town, in which it is portrayed as a the hipsterest most l337 joint for the securi-hacker community. The worst part is that it mentions my coffee shop. I'll never feel safe using wi-fi again. (Actually, I usually limit myself to consumption of paper based information at coffee shops. But that's just me.) (And the coffee shop is not the one that is fully populated with jaded 21 year old grad students.) (It's the other one.)
Extra tooth
I agree with this comment to this Dark Reading article on the e-Gold dust-up. However, I believe that the phrase "going for the juggler" was an error. I've generally expressed the sentiment as "going for the juggalo." The powers that be are generally in a state of going for the juggalo.
Romanian toothpaste from Jessamyn
Posted by
Dutcher Stiles
at
3:34 PM
0
comments
![]()
Thursday, April 26, 2007
Go Ask Alec Baldwin

SSL apostate Ian G. refers to an article on estimation of loss due to a privacy breach.
I think we are measuring the wrong thing, and operating on these assumptions is dangerous.
From the article, a Forrester analyst says:
"After calculating the expenses of legal fees, call centers, lost employee productivity, regulatory fines, stock plummets, and customer losses, it can be dizzying, if not impossible, to come up with a true number."The $90 - $305 range smacks of too much precision and not enough accuracy. Only software project managers can get away with ranges like that. These numbers are more harmful that worthwhile. Most of these factors are not driven by record count (legal fees, stock plummets or lost productivity). Record specific costs are generally lower (call center and postage - and if you lose enough records, you don't even have to mail notices). So let's just call it BTUs per furlong and call it a day. And I don't think "customer losses" is as important in assessing the risk as "losses to customer."
The next Forrester quote underlines the problem I have with the general corporate thinking about privacy breaches:
"Previously, when a company had a data breach, a response team would fix the problem and test the mitigation, then the company would resume normal activities. Now we have to spend time on public relations efforts, as well as assuring both customers and auditors that new processes are in place to guard against such breaches in the future."The reason you could get away with just fixing it and moving on was because the company did lose anything it owned. What it lost was owned by its customers. Losing one bit of highly sensitive data about one litigious customer could cause more damage that a dozen laptops filled with the SSNs of 10 million people.
It's the "loss to the customer" that will drive your high dollar PR and legal efforts, which have scale, and can dwarf your call center and postage costs in an afternoon.
I'd like to take the data, rehash it according to type of breach, sensitivity of data and litigiousness of customer. Then I think you'd start on the road to a meaningful metric.
Posted by
Dutcher Stiles
at
6:35 PM
0
comments
![]()
Labels: disclosure laws, identity theft, privacy, sb1386, security
Tuesday, April 24, 2007
The Red, Yellow and Green Legos of Judgment

I'm out here in Coyote and Roadrunner land, knee deep in internal auditing. I co-presented yesterday on privacy, as a co-author of an Institute of Internal Auditing publication.
It's been a interesting couple of days, driven in part by the isolation of the location. As attractive as a golf/casino resort may sound, it's not so groovy if you don't golf, don't gamble and didn't have the foresight to rent a car. I can meditate on the cacti, and read. I packed a couple of books to get me in and out of the Internal Auditing mindset: The Digital Person by Daniel Solove (highly recommended), a Kierkegaard anthology (because what is auditing but fear, trembling, and sickness unto death?) and Nassim Nicholas Taleb's The Black Swan (I've been alternately writing "YES!" and "BULLSH*T!" in the margins. (It's my policy to keep the margins safe for work.))
But this morning I had my own inverse Damascus moment, as Bill Power (if that is his real name) of the PCAOB was giving the assembled throng his information technology application auditing method, as demonstrated through a manufacturing case study. It was interesting enough as analysis of manufacturing financial systems go (yes, exactly that interesting), but at the end of his case study it seemed to me that he just plopped Red, Yellow and Green Legos into the risk spaces in his spreadsheet, and chalked it up to judgment. In fact, one of the slides read something like "RISK ASSESSMENT IS ALL JUDGEMENT" (I'd quote directly, but his presentation is not on the conference CD-ROM. I do remember he spelled "Judgment" with two "E"s.)
O.k. Sure. Risk assessment without judgment is pretty worthless. And auditors have an obligation to use their judgment to assess risk. Nonetheless, it doesn't seem worthwhile to go through all this spreadsheetin' and flowchartin' just to get to the point where you pull red, yellow and green Legos out of your velvety Audit Sack of Judgment and snick-snack them on financial information systems and processes master control grid. How about the stuff you don't understand well enough to apply judgment? I'm getting the idea that it's called "Out of Scope."
At what point does "judgment" intersect with "caprice"?
Go ahead, call me naive (if you haven't already). But it's getting dark, and I'm going to see if the cows come back to the hotel parking lot again tonight. This time I'll be ready.
Photo courtesy of The Bill.
Posted by
Dutcher Stiles
at
6:17 PM
1 comments
![]()
Labels: internal auditing, risk assessment, SOX
Tuesday, April 17, 2007
Apocalypse Pooh
It's a grim world around us. A mass murder turns into a cynical ploy to promote and condemn any issue you care to name, or exploit the grief for naked profit.
How can I deal, in the short term, except for a brief absurd laugh?
Thanks to the Moonshine Mountaineer for the Youtoobage.
Posted by
Dutcher Stiles
at
5:45 PM
0
comments
![]()
Labels: Pooh
Wednesday, April 11, 2007
Sweet Fancy Moses

Lots of odd stuff (mostly from Pogo & Fergie):
Why Justice Went Blind The courthouse security folks in El Paso County can see you nekkid.
"The new machine will not replace the metal detectors already in use at the judicial complex. Instead, it will replace two of the security guards who use wands to screen entrants that set-off the metal detectors. The board of commissioners estimates by replacing the guards with the body scanner the county will save $64,704 a year."
Outstanding! You can see my ass, and fire two guards!
Consumers Are JUMPY! "77 percent of Javelin's respondents said they intend to stop shopping at sites that have experienced data breaches." Well, I'm firing Trans Union, the IRS & Travis County!
ID Theft-O-Meter! - Hold on, where do I put the cost of monitoring my own credit, talking to the police, time spent in jail on false arrest, higher interest rates after a company is careless with my own date? Oh... It for the corporations that lost it. The REAL victims!
NETCOSM! - Just plain cool. I remember something similar years ago, where you used DOOM maps to kill processes on FreeBSD. Yes! PSDOOM.
Posted by
Dutcher Stiles
at
7:28 PM
0
comments
![]()
In defense of controls
Alex is pretty down on ISO 17799.
I think the reasons are that he sees organizations substituting ISO 17799 for risk management FAIR style. Instead of calculating a realistic, customized risk profile, an organization pulls ISO 17799 (or COBIT, though COBIT is less specific to security) off the shelf. The specific controls in the 10 areas are implemented, and therefore they are secure, and risk-free. However, a focus on these areas may not appropriately address the real risk to the organization, and may result in inefficient and ineffective use of resources. (I hope he'll correct me if I'm wrong.)
I think he's right if that is how the standards are implemented, but it is not necessarily the only way they can be used. I'm thinking that if used properly, ISO 17799 could help in implementing controls to reduce the risk identified. He cites an example of using metrics to manage patches. I see it this way:
Risk analysis identifies areas for control.
High value assets on exposed servers are vulnerable to complete compromise from any weak-ass hax0r wannabe, because of well known problems in the OS. The vendor has issued patches, and continues to issue patches on a routine basis.
The control is implemented.
Defining the control is where ISO and Cobit would come in. Once you have decided that it should be done, it can answer the question of how. If others have discovered a way to control the situation that works reliably, I don't see why you wouldn't want to use it. Engineers and accountants do it all the time. At the same time, it must be optimized to meet not only your specific risks, but also your environment and culture. Striking the balance between the universal and specific is the challenge that standards face.
The effectiveness of the control is measured.
A metric could be used to determine the effectiveness of the control, as well as the appropriateness. If you are unable to tell if a control is functioning, it is hard to tell if it is effective. If the server team does not adequately test the patches, or places lower risk items higher in the work queue, your risk is not being mitigated when you think it should be. An armed guard isn't an effective control if he's asleep all the time.
The way I see it, risk assessment is necessary to prioritize controls. Controls are used to manage risk. And metrics are used measure the effectiveness of controls. There are multiple ways any of these can go wrong, but it's a beautiful evening and my motorcycle needs exercise.
Posted by
Dutcher Stiles
at
3:34 PM
3
comments
![]()
Thursday, April 5, 2007
Invincible
New York Magazine article "The Young Invincibles: A Generation Uninsured" discusses the way uninsured 20-30 year olds in New York deal with health risks (link and commentary from Concurring Opinions.)
The article is interesting study of people who do not participate in the most common health risk management strategy: insurance. Unable to afford it, or "rationally" choosing to be uninsured, they have created their own strategies to minimize exposure. Curtailing snowboarding activities (only the half pipe), daily brushing, and yoga are balanced with careers as bike messengers and retailers. There is a wide range of risk appetites: the bike messenger who feels that "helmets are cumbersome," and artist who eschews bicycling completely. Maintenance and prevention are expensive or inconvenient, so the Invincible's focus is on the severe or catastrophic cases.
Are there corporations out there that believe themselves to be "invincible"? Is this the sort of attitude that prevents real security from becoming embedded into a corporate culture? No doubt possible. Also likely is the false sense of security associated with "compliance" as a risk mitigation technique. SOX is like a bicyclist's helmet ("too cumbersome"). PCI is like brushing your teeth every day. No one condemns daily brushing, but it won't help when you get a kick in the teeth.
(I recall my own period of "invincibility." Working without insurance as a deckhand on a towboat on the Ohio, Tennessee and Cumberland Rivers, I didn't see the dangers of hopping from barge to coal soot covered barge, lugging 90-lb ratchets and wire, all risk mitigated by my Redwings and a bump hat. Not until a near death experience while epoxying the inside of a fresh water tank did I think "Hey, what if I get crushed? What if my brain is actually damaged, and no one will ever get my jokes?" Then I sought less perilous employment. With a health and dental plan. So I found my way to the Guild of the Green Eyeshade.)
Men's 8-inch work boot with metatarsal guard courtesy Redwing.
Posted by
Dutcher Stiles
at
3:58 PM
0
comments
![]()
Labels: compliance, risk assessment, risk management
Wednesday, April 4, 2007
One Man's Trash

The righteous fury of Texas Attorney Abbott was last month stymied by an elite cadre of county clerk ninjas who conjured a shambling legislative behemoth to crush his valiant effort to protect the privacy of Texans.
Abbott screwed his courage to the sticking place, and was not to be denied.
Laying down the latex gauntlet, and taking a dog-eared chapter from a 1987 hacker's playbook, he strikes a meaty vein of SSN laden paydirt in the dumpsters of Radio Shack, a beauty school and a talent agency.
Having done of bit of professional dumpster diving myself, I laud the AG's efforts. Nothing increases a man's disposal awareness more than seeing a dude in a suit digging through garbage.
No doubt the most disturbing part of the story is the sample recovered receipt displayed on the AG's website. I mean, $99.97 for a 2 GB portable drive? With $17.99 for a 12 month warranty? Now that's obscene.
Illustration courtesy Speas.
Posted by
Dutcher Stiles
at
5:00 PM
0
comments
![]()
Labels: consumer, identity theft, internal auditing, physical security, texas
Friday, March 30, 2007
Auditing Privacy Part 2 - Risk Assessment of Data Loss
The easy way to assess privacy risks is to focus on the impact of data theft to the organization by including the private data as a corporate asset. There are well documented methods to identify the vulnerabilities in means of collecting, storing and sharing the data. Similarly, there are methods to identify and list the data's threats (hackers, "insiders," and negligent loss). The impacts will likely shake out along the lines of direct costs (postage, call center, other incident response costs), potential legal and regulatory actions and reputation damage. (For an example, Protegrity assessed the TJX data breach at $1.7 billion, though TJX was not strictly a privacy issues, it has parallels*).
This would be the easy way, but may not result in the most accurate results. The problem lies in identifying the impacts of a privacy breach. The attribute of “privacy” assigned to the data is what makes the data valuable, and worthy of protection. However, "privacy" is not an attributed that belongs to the corporation, but to the individual the data describes. So an assessment of risk to the corporation of privacy loss should start at looking at the impact of the loss to the individual.
Why do many corporations, when disclosing losses of tremendous amounts of data, appear to suffer only short term damage to their reputation. I posit that the potential damage to a corporation is proportional to the actual real damage to privacy of the individuals described in the lost damage. (See Guin v Brazos)
The real impact of a privacy incident on individuals has been hidden behind a cloud of security vendor fear mongering and media induced panic. The common problems with the data is equating data loss with a privacy breach. Identity theft properly defined is likely a higher impact, lower frequency event than is commonly reported.
The SB1386-style disclosure laws have been a boon to identifying the frequency of data loss, but the information that has to be disclosed does little to help identify the impact. An auditor concerned strictly with compliance would have to place equal risk to any loss of private data. But the auditor should take the risk assessment to the next step and focus on the individuals, identifying the risks that lead to actual harm to the privacy of individuals. Compliance risk is equivalent for the loss of a laptop carrying an encrypted database of private data and the same databases being heisted off a web server unencrypted by a criminal with the intent to exploit the identities. The real risk to the privacy of the individuals described in the database is clearly different.
Beyond the risk of a data loss, the auditor should also consider the equally important risks of the collection of private data and the dossier-ification of data. More on that later.
*Why the high risk to TJX? Though not strictly a privacy issue, the damages related are an issue of a loss to a third party - the banks - rather than TJX itself.
"Some would call this good fortune" from s2art
Posted by
Dutcher Stiles
at
3:55 PM
0
comments
![]()
Labels: identity theft, internal auditing, privacy, risk assessment
Tuesday, March 27, 2007
Impacted Molars II

Occlusal
Panopticonistas Cyveillance say ID theft is so bad, we are all going to die. Seems like shutting down copyright scofflaws got a little too Web 1.0 for them, so they've unleashed their vicious crawling spiders on a search for contraband identities. And guess what they found out? EVERYBODY'S IDENTITY IS ALREADY PWN'D! Now that they've collected this data, I'm curious as to what are they going to do with all those credit card numbers, SSNs and mothers' maiden names. Did they help shut down the sites hosting the illicit data? Did they notify the victims? This sort of research is on an odd ethical footing. I hope they get it all sorted before they do their research on other forms of digital contraband.
Distal
California Secretary of State Debra Bowen kicks ass in the name of privacy for Californians. She gets privacy, and maybe even cares about the citizens of California. I wish she could impart some of her knowledge to the Texas county clerks.
Mandibular
CDT publishes their draft Privacy Principles for Identification. Seem pretty much like Fair Information Practices to me, which is not necessarily a bad thing.
Fake Teeth Resting on Image of Monk courtesy jsdart
Posted by
Dutcher Stiles
at
7:30 PM
0
comments
![]()
Labels: compliance, ethics, fraud, identity theft, privacy, ssns
Monday, March 26, 2007
Insider Threat Assessment
Posted by
Dutcher Stiles
at
6:36 PM
0
comments
![]()
Labels: bsg, insider threat
Thursday, March 22, 2007
Panopticon Enabled Desktops Increase Productivity!
![]()
From Dark Reading, the joys of workforce monitoring software with Ascentive!:
"We call it 'workforce activity management,'" says Schran. "Our latest edition provides all the insight necessary to eliminate time-wasting, increase productivity, and protect private company data."Or, in the words of Ascentive's VP of Customer Relations Jeremy Bentham,
More from Dark Reading:
Morals reformed - health preserved - industry invigorated - instruction diffused - public burthens lightened - Economy seated, as it were, upon a rock - the gordian knot of Gramm Leach Bliley and Sarbanes-Oxley are not cut, but untied - all by a simple idea in Software Architecture!
Perhaps even more importantly, employee monitoring tools can deter workers from insider activities such as data theft or unauthorized file access, Schran adds. "If your employees are downloading files to a USB device, our software will record that action," he says. "Our data has already been used in evidentiary proceedings in court."
But I prefer the hot buzz on this product from their EU Product Evangelist Michel Foucault:
The heaviness of the old 'houses of security', with their fortress-like architecture, could be replaced by the simple, economic geometry of a 'house of certainty'. The efficiency of power, its constraining force have, in a sense, passed over to the other side - to the side of its surface of application. He who is subjected to a field of visibility, and who knows it, assumes responsibility for the constraints of power; he makes them play spontaneously upon himself; he inscribes in himself the power relation in which he simultaneously plays both roles; he becomes the principle of his own subjection. By this very fact, the external power may throw off its physical weight; it tends to the non-corporal; and, the more it approaches this limit, the more constant, profound and permanent are its effects: it is a perpetual victory that avoids any physical confrontation and which is always decided in advance.
And they say security software people don't read post-structuralist French philosophers. Heck, Foucault is all around you! I running a Jacques Derrida Packet Sniffer & Deconstructor right now! Or am I?
Posted by
Dutcher Stiles
at
3:51 PM
0
comments
![]()
Labels: insider threat, panopticon, privacy
Tuesday, March 20, 2007
Auditing Privacy Part 1 - Ethics and the Canon
It would comfort many compliance auditors to discover the ultimate checklist and tear after their organization's privacy program, collecting tick marks and developing the dreaded deficiency finding. I say to them, "Google is your friend." For the more enlightened internal auditor, the first step in evaluating their organizations privacy practices should be a step back.
The Canon
There are best practices, and there are benchmarks. There are torts, laws, and rational fear of the irrational regulator. However, for most every auditable area there is also The Canon. Take a file to the gilded crust of Sarbanes-Oxley and the PCOAB (and all their works and all their ways), you eventually uncover the Generally Accepted Accounting Principles. Take a snowblower to the myriad layers of dust and ash of the Code of Federal Regulations. If you squint and hold your head just right, you'll see a vague outline of the Decalogue. And somewhere below ornate filigree and baroque ornamentation of HIPAA, Gramm Leach Bliley and SB1386 is the shape of the Fair Information Practices of the US Department of Health, Education and Welfare, 1973.
From the link above, here are the five practices of the modern privacy canon:
- Collection limitation
- Disclosure
- Secondary usage
- Record correction
- Security
The 10 AICPA's Generally Accepted Privacy Principles
The OECD Guidelines on the Protection of Privacy and Transborder Flows of Personal Data
The Ethos
Like the Torah, the Sermons of Buddha, the Qur'an, the Gospels, or Fermat's Principle, a canon is only meaningful if applied. You must ask the CEO, the CIO, the Chief Marketeer, the General Counsel, and listen, and interpret their answers accordingly. Are the principles used as values to guide their decisions, obstacles to be worked around, or are they simply unknown? Read your corporate policies regarding privacy. Do you see in them evidence of the Fair Information Practices, or do they appear to be more oriented to a specific set of industry specific regulations? Interview the folks who handle the data. Do they treat the data with the care they would treat their own? The answers to these questions will begin to lead you to determining if your organization has the ethical basis for a privacy program.
What Does This Mean?
A compliance oriented organization may maintain reasonable concordance with Fair Information Practices without even knowing what they are. However, the organization may be reactive, and inefficient. The organization's privacy direction will be dictated by outside entities, rather than developed within.
A organization with a firm foundation in privacy practices, coupled with an ethic duty to privacy, will be more efficient, more effective, and retain a better reputation in the face of an incident.
Posted by
Dutcher Stiles
at
3:26 PM
0
comments
![]()
Labels: compliance, internal auditing, privacy, regulations
Monday, March 19, 2007
I Am Not A Cop

A couple posts on the role of internal audit in the information security controls of a company got me thinking.
First, Anton describes an auditor as "policing agent" model:
- InfoSec develops controls.
- Operations operationalizes them.
- Audit goes around with a checklist to make sure they got done
The issue I have with this model is that if what InfoSec develops are inadequate, they could still be well implemented. InfoSec should take ownership in the controls, and insure they are implemented and monitor their performance after they are implemented. When the auditor comes along, he or she should be looking not only at the implementation, but if the system as designed by InfoSec achieves the requisite goals of risk reduction acceptable to the board. Unlike the crime, systems development or drug prescription analogies, information security is an ongoing management process.
So I'm looking through rose colored glasses rather than my usual green eyeshade, but I'm not going to play Kavenaugh to bunch of Mackeys.
Posted by
Dutcher Stiles
at
6:27 PM
0
comments
![]()





